The lightweight, AI-powered network intrusion prevention system, detecting and blocking threats in real time. Explore the code on github.
Stage 1
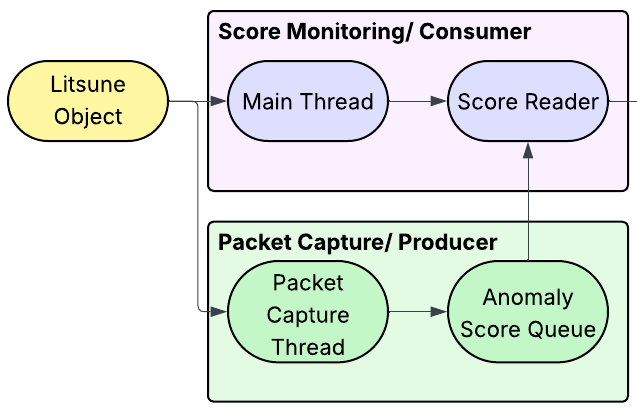
Litsune is the product of multiple interconnected systems working together to achieve a shared goal. First, Litsune captures incoming traffic using PyShark. Simultaneously, the main thread reads these packets and extracts data such as protocol, frame length, arrival time, and source and destination MAC and IP addresses.
Stage 2
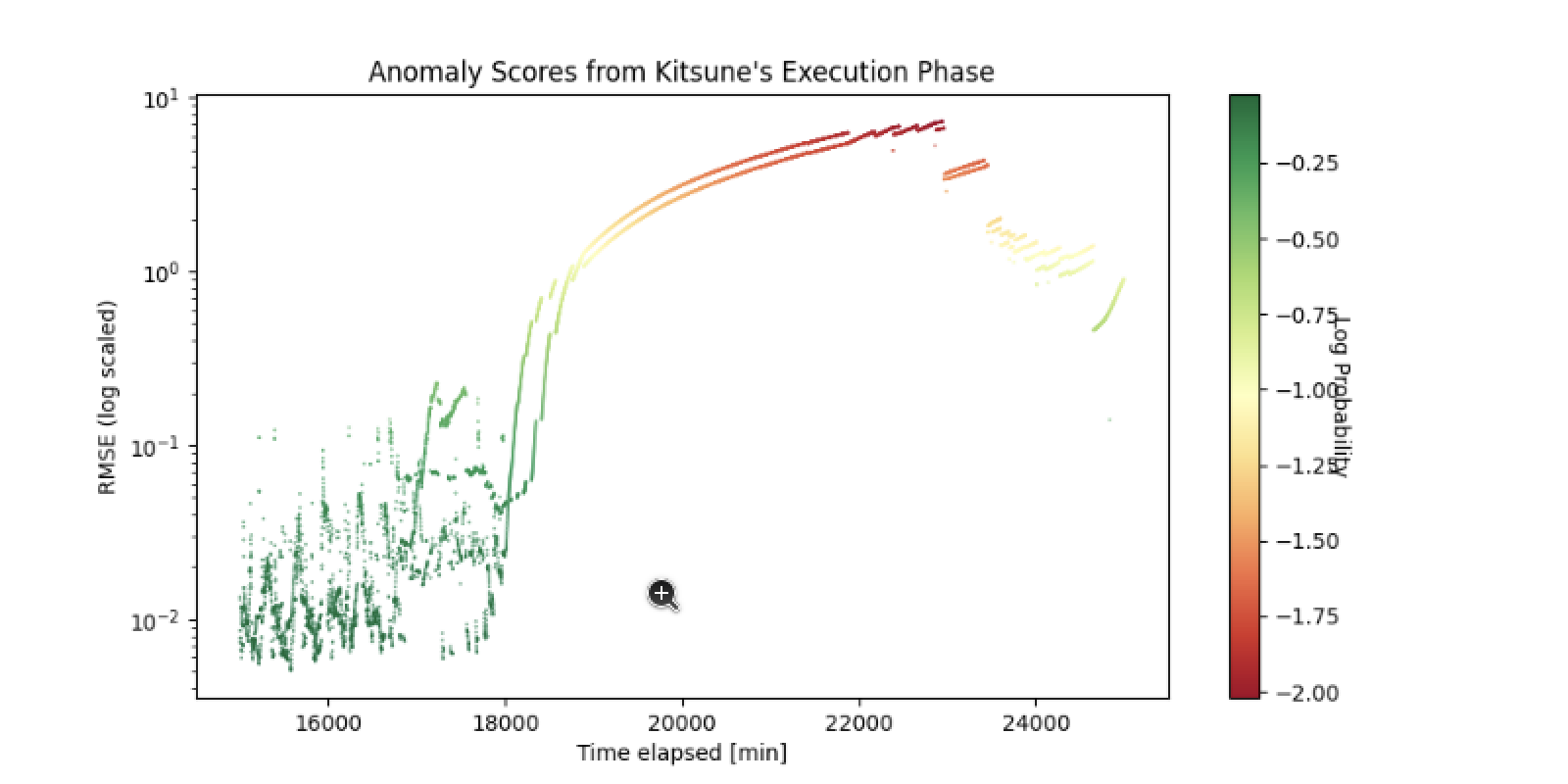
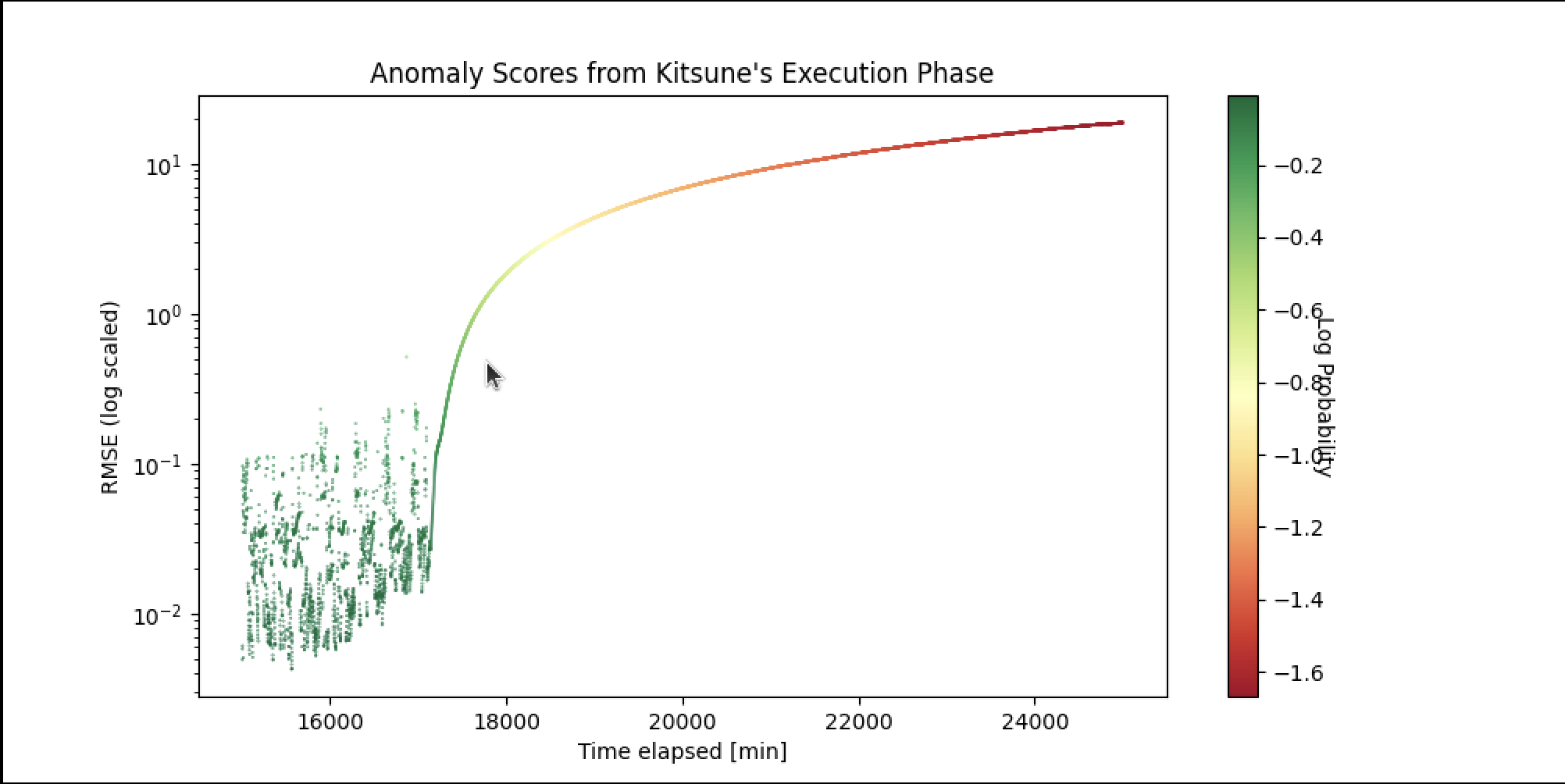
Next, this data is piped into a network of autoencoders called KitNET, developed by a team from Ben-Gurion University of the Negev. KitNET takes in information from the packets and outputs anomaly scores, or probabilities that any given packet is anomalous. It enters a two-step training period where it distributes the features across a number of neural networks called autoencoders, and learns the anomaly probability values associated with "regular" traffic.
Stage 3
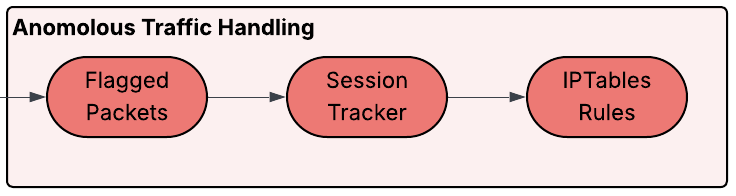
Finally, the model goes into execution mode. An error score threshold is determined probabilistically from among the 50 highest anomaly scores found during the training period, and any traffic that exceeds this threshold is flagged. If a certain number of flagged packets from the same source is reached, Litsune triggers an IPTables rule that temporarily blocks all traffic from that source.
Takeaways
The strength of this project is that it is lightweight and runs very effectively on systems with limited computing power. This tool's ability to train on real-time traffic and continuously learn as traffic patterns change means that it can be implemented in just about any environment on just about any device, and can reliably detect many different types of attack, including DoS, Portscan, IP Spoofing, and more!
Litsune is built off of Kitsune, a project by Yisroel Mirsky, Tomer Doitshman, Yuval Elovici, and Asaf Shabtai. This project is detailed in Kitsune: An Ensemble of Autoencoders for Online Network Intrusion Detection (doi: 10.14722/ndss.2018.23204).